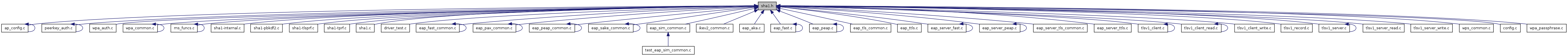
Go to the source code of this file.
Defines | |
| #define | SHA1_MAC_LEN 20 |
Functions | |
| int | hmac_sha1 (const u8 *key, size_t key_len, const u8 *data, size_t data_len, u8 *mac) |
| int | hmac_sha1_vector (const u8 *key, size_t key_len, size_t num_elem, const u8 *addr[], const size_t *len, u8 *mac) |
| int | pbkdf2_sha1 (const char *passphrase, const char *ssid, size_t ssid_len, int iterations, u8 *buf, size_t buflen) |
| int | sha1_prf (const u8 *key, size_t key_len, const char *label, const u8 *data, size_t data_len, u8 *buf, size_t buf_len) |
| int | sha1_t_prf (const u8 *key, size_t key_len, const char *label, const u8 *seed, size_t seed_len, u8 *buf, size_t buf_len) |
| int __must_check | tls_prf (const u8 *secret, size_t secret_len, const char *label, const u8 *seed, size_t seed_len, u8 *out, size_t outlen) |
| int hmac_sha1_vector | ( | const u8 * | key, | |
| size_t | key_len, | |||
| size_t | num_elem, | |||
| const u8 * | addr[], | |||
| const size_t * | len, | |||
| u8 * | mac | |||
| ) |
hmac_sha1_vector - HMAC-SHA1 over data vector (RFC 2104) : Key for HMAC operations : Length of the key in bytes : Number of elements in the data vector : Pointers to the data areas : Lengths of the data blocks : Buffer for the hash (20 bytes) Returns: 0 on success, -1 on failure
| int pbkdf2_sha1 | ( | const char * | passphrase, | |
| const char * | ssid, | |||
| size_t | ssid_len, | |||
| int | iterations, | |||
| u8 * | buf, | |||
| size_t | buflen | |||
| ) |
pbkdf2_sha1 - SHA1-based key derivation function (PBKDF2) for IEEE 802.11i : ASCII passphrase : SSID : SSID length in bytes : Number of iterations to run : Buffer for the generated key : Length of the buffer in bytes Returns: 0 on success, -1 of failure
This function is used to derive PSK for WPA-PSK. For this protocol, iterations is set to 4096 and buflen to 32. This function is described in IEEE Std 802.11-2004, Clause H.4. The main construction is from PKCS#5 v2.0.
Definition at line 80 of file sha1-pbkdf2.c.
| int sha1_prf | ( | const u8 * | key, | |
| size_t | key_len, | |||
| const char * | label, | |||
| const u8 * | data, | |||
| size_t | data_len, | |||
| u8 * | buf, | |||
| size_t | buf_len | |||
| ) |
sha1_prf - SHA1-based Pseudo-Random Function (PRF) (IEEE 802.11i, 8.5.1.1) : Key for PRF : Length of the key in bytes : A unique label for each purpose of the PRF : Extra data to bind into the key : Length of the data : Buffer for the generated pseudo-random key : Number of bytes of key to generate Returns: 0 on success, -1 of failure
This function is used to derive new, cryptographically separate keys from a given key (e.g., PMK in IEEE 802.11i).
| int sha1_t_prf | ( | const u8 * | key, | |
| size_t | key_len, | |||
| const char * | label, | |||
| const u8 * | seed, | |||
| size_t | seed_len, | |||
| u8 * | buf, | |||
| size_t | buf_len | |||
| ) |
sha1_t_prf - EAP-FAST Pseudo-Random Function (T-PRF) : Key for PRF : Length of the key in bytes : A unique label for each purpose of the PRF : Seed value to bind into the key : Length of the seed : Buffer for the generated pseudo-random key : Number of bytes of key to generate Returns: 0 on success, -1 of failure
This function is used to derive new, cryptographically separate keys from a given key for EAP-FAST. T-PRF is defined in RFC 4851, Section 5.5.
Definition at line 35 of file sha1-tprf.c.
| int __must_check tls_prf | ( | const u8 * | secret, | |
| size_t | secret_len, | |||
| const char * | label, | |||
| const u8 * | seed, | |||
| size_t | seed_len, | |||
| u8 * | out, | |||
| size_t | outlen | |||
| ) |
tls_prf - Pseudo-Random Function for TLS (TLS-PRF, RFC 2246) : Key for PRF : Length of the key in bytes : A unique label for each purpose of the PRF : Seed value to bind into the key : Length of the seed : Buffer for the generated pseudo-random key : Number of bytes of key to generate Returns: 0 on success, -1 on failure.
This function is used to derive new, cryptographically separate keys from a given key in TLS. This PRF is defined in RFC 2246, Chapter 5.
Definition at line 37 of file sha1-tlsprf.c.