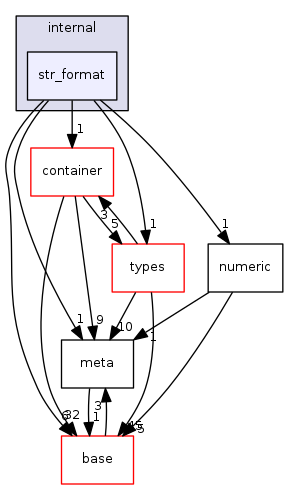
Directory dependency graph for str_format:
Files | |
| file | arg.cc [code] |
| file | arg.h [code] |
| file | arg_test.cc [code] |
| file | bind.cc [code] |
| file | bind.h [code] |
| file | bind_test.cc [code] |
| file | checker.h [code] |
| file | checker_test.cc [code] |
| file | convert_test.cc [code] |
| file | extension.cc [code] |
| file | extension.h [code] |
| file | extension_test.cc [code] |
| file | float_conversion.cc [code] |
| file | float_conversion.h [code] |
| file | output.cc [code] |
| file | output.h [code] |
| file | output_test.cc [code] |
| file | parser.cc [code] |
| file | parser.h [code] |
| file | parser_test.cc [code] |